Agentic AI vs. Your API
Understand the shift from scripted bots to reasoning AI agents and how to adapt your security strategy for this new reality.
Understand the shift from scripted bots to reasoning AI agents and how to adapt your security strategy for this new reality.
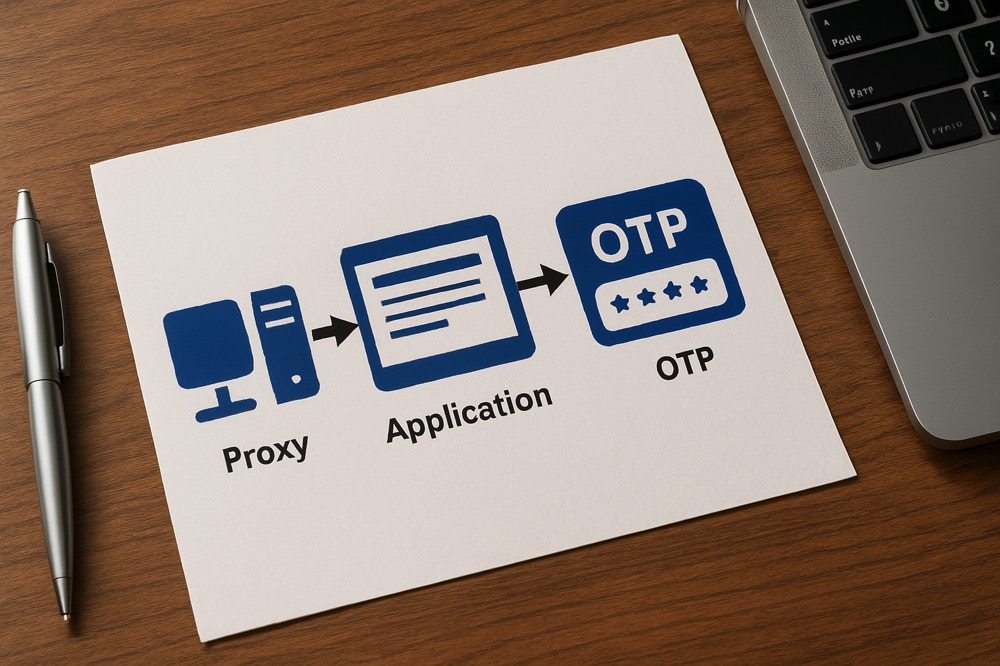
A deep dive into how credential stuffing attacks work, the tools used, and how to build a multi-layered defense.

With nearly half of all internet traffic being automated, a robust bot management strategy is essential. This article explores the key considerations for effective bot detection, classification, and response in the face of evolving threats.

Learn to classify bots into good, bad, and grey categories and apply the right management strategy for each.

Bots are used in both security and nonsecurity attacks. Identity and access management leaders must build a strong business case for a bot management capability or their organizations will incur avoidable losses due to account takeovers and also be unprepared to manage the risks introduced by customers using AI agents.

Analysis of attempts to exploit a recent Share Point zero day vulnerability reveal network fingerprinting and classification is a robust defense.

The proliferation of residential proxy networks has undermined traditional IP-based security, enabling attackers to bypass protection measures while appearing as legitimate users.

AI agents with reasoning capabilities like DeepSeek are revolutionizing exploit development, marking the end of traditional security approaches based on static rules and patterns.
How Peakhour's contextual security aligns with Visa's data-driven risk management approach in the 2025-2028 Security Roadmap.

How residential proxy networks may have enabled DeepSeek to bypass AI platform protections, leading to Nvidia's historic market value loss
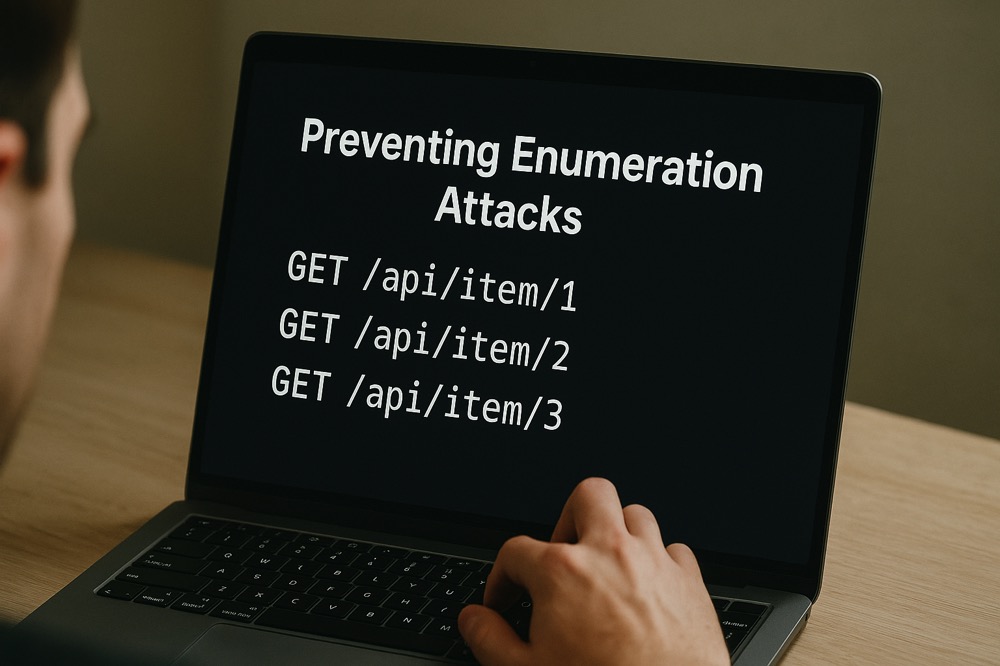
An analysis of how Peakhour's solutions help prevent enumeration attacks, aligning with Visa's Security Roadmap 2025-2028 priorities.

Learn how MTU fingerprinting reveals VPN usage, mobile connections, and network technologies through TCP handshake analysis. Discover practical SQL techniques for dynamic network intelligence.

Anti-detect browsers represent one of the most sophisticated threats facing modern web applications and APIs. Learn how these tools work, why they pose a significant threat to application security, and how modern security platforms can detect and mitigate their use.

Learn how distributed bot networks using residential IPs are evolving to evade traditional fraud detection

Comprehensive analysis of AI-powered cyber threats and how modern application security platforms defend against machine learning-driven attacks. Learn advanced defence strategies for the AI cybersecurity arms race.

Your anti fraud IP Intelligence service is no longer fit for purpose. Learn about the challenges in detecting residential proxies and why traditional methods don't work.

An in-depth look at the growing threat of credential stuffing attacks on Australian businesses, including recent case studies, defense challenges, and practical recommendations.

Examine why current security solutions fail to detect and mitigate threats from residential proxies, and the need for comprehensive protection strategies.

Explore the complexities of residential proxy detection and its impact on organisational risk, with a focus on quantifying the threat and reframing security approaches.

Multi-factor authentication alone cannot protect against sophisticated AI-powered attacks and residential proxy networks. Learn how modern application security platforms provide comprehensive account takeover prevention through multi-layered defence strategies.

An analysis of Peakhour's role in addressing key cloud security categories identified in recent industry analysis, demonstrating its comprehensive approach to modern cloud security challenges.

Comprehensive guide to breached credentials protection within modern application security platforms. Learn how to defend against credential stuffing attacks using advanced risk profiling and contextual security measures.

How advanced rate limiting protects modern applications and APIs from sophisticated threats including proxy networks, distributed attacks, and automated abuse in enterprise security environments.

Understand CVSS by examining the Atlassian CVE-2023-22515 and CVE-2023-22518.

An in-depth exploration of EPSS, its data-driven approach to assessing cybersecurity threats, and how it complements CVSS.

Reviewing the CVSS an EPSS CVE scoring systems in light of the Atlassian Confluence-Aggedon

An in-depth exploration of the JA4+ network fingerprinting method, its applications, and its role in cybersecurity.

ModSecurity's end-of-life marks a pivotal moment in application security evolution. Discover how modern Application Security Platforms are advancing beyond traditional WAF approaches to provide comprehensive protection for web applications and APIs at the edge.

Comprehensive guide to APRA cybersecurity requirements for Australian financial institutions. Learn how application security platforms help meet CPS 234 compliance and Information Security Manual guidelines for protecting financial services infrastructure.

A comprehensive breakdown of the HTTP/2 Rapid Reset flaw and guidance on bolstering defences against potential DDoS attacks.

A comprehensive look at OpenBullet, its capabilities, and the implications for cybersecurity in the face of its misuse.

Analysis of the Microsoft 365 DDoS attack by Storm-1359 reveals critical lessons for enterprise application security platforms. Learn advanced Layer 7 DDoS protection strategies and rate limiting techniques for modern applications.

Residential proxy malware, and its implications for traditional cybersecurity measures, emphasising the need for evolving threat detection and mitigation strategies.

Explore residential proxies within the context of the MITRE ATT&CK framework, highlighting the security implications and ethical considerations.

Comprehensive analysis of residential proxy threats and detection strategies for modern application security platforms. Learn how sophisticated threat actors use residential proxies to bypass traditional security measures.

Deep dive into Robust Random Cut Forest (RRCF) implementation for real-time anomaly detection in Application Security Platforms. Learn how advanced machine learning algorithms enhance threat detection and automated response capabilities.

This article explores the use of Double Median Absolute Deviation (Double MAD) for anomaly detection in time series data, particularly in skewed or non-symmetric distributions.

Discusses strategies for scaling the Robust Random Cut Forest (RRCF) algorithm for large-scale anomaly detection, including using summary statistics, buffering input, and parallelisation.

Explores various thresholding techniques like Median Absolute Deviation (MAD), Min/Max, and Z-Score for interpreting Robust Random Cut Forest (RRCF) anomaly scores, crucial for classifying data points as normal or anomalous.

Comprehensive guide to IP threat intelligence for modern application security platforms. Learn how managed IP reputation lists and threat intelligence feeds protect applications from known malicious sources and emerging threats.

Comprehensive guide to intelligent rate limiting for modern application security platforms. Learn how sophisticated rate limiting protects APIs and web applications from abuse, DDoS attacks, and automated threats whilst maintaining optimal user experience.

Comprehensive guide to enterprise bot management and advanced countermeasures for protecting applications against sophisticated malicious bot threats. Learn proven strategies for bot detection, mitigation, and automated defence systems.

Comprehensive guide to application performance optimisation with integrated security testing. Learn how modern Application Security Platforms deliver superior performance whilst maintaining robust threat protection for contemporary applications.

Introducing Instant Alerts, a new feature for receiving emails or SMS alerts when events happen on your site.
© PEAKHOUR.IO PTY LTD 2025 ABN 76 619 930 826 All rights reserved.